This particular visitor submit is by Chris Crider, Safety Techniques Engineering Chief for Cisco US Public Sector

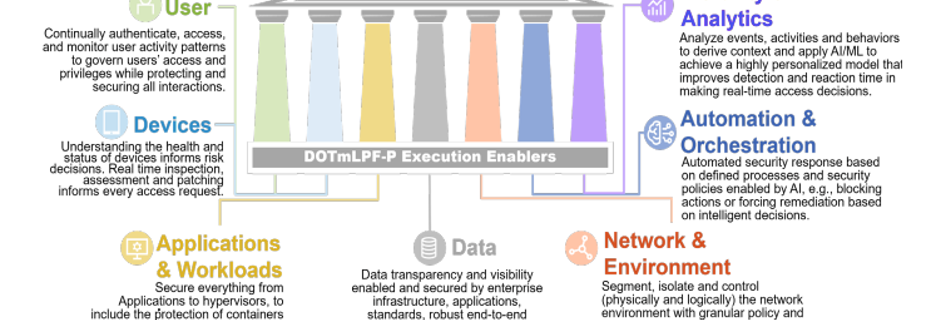
In terms of Zero Belief frameworks and ideas, few organizations are as complete because the US Division of Protection (DoD). In 2022, the DoD launched their seven-pillar technique to articulate their vital cyber capabilities and actions related to Zero Belief ideas (Determine 1), whereas additionally aligning the purposeful rollout of these capabilities with a focused timeline of execution of the fundamentals by way of 2027.
What’s Comply to Join?
One of many capabilities within the Gadgets pillar of the DoD Zero Belief Technique is Comply to Join (C2C), an NDAA mandate and a Protection Info Techniques Company (DISA) program setup to watch and handle authorities endpoints and their well being, plus to have an effect on their authorization into the surroundings primarily based on an ongoing set of endpoint standards. The scope of the C2C program is an incredible enterprise by itself. Nonetheless, this system’s extent doesn’t account for person and system attribution to classes or habits inside every session, which will also be made by way of a typical set of instruments within the journey to Zero Belief maturity.
The Comply to Join program is a bridge to Zero Belief entry. So, system authentication and authorization must account for not solely person gadgets but in addition non-user gadgets. That is very true for the reason that huge worlds of the Web of Issues (IoT) and Industrial Web of Issues (IIoT) have entered the highlight resulting from cyber-attacks and a scarcity of emphasis on non-user gadgets like SCADA programs, site visitors sensors, and safety cameras.
Comply to Join and system habits
Because the IoT and IIoT have now turn out to be key gateways for intrusion, system well being and least-privilege authorization should now be complemented with an understanding of system habits and exercise. For instance:
- Can a company establish a tool (like a digicam)?
- Does a tool exhibit uncommon exercise for its function (like attempting to connect with an adversarial community)?
- Or much more merely, from an operational perspective, is a licensed endpoint on one community making an attempt to connect with a special community classification?
Making use of Zero Belief ideas like these to authorities networks helps companies correctly establish and authorize (or deny) any person and system attempting to entry their community. Simply as importantly, it allows your company to repeatedly monitor and attribute the habits of an entity in your community. This allows you to rapidly and precisely take applicable actions to remain safe.
Cisco’s safety portfolio helps authorities organizations enhance their Zero Belief maturity by facilitating safe communications from endpoint to software. This consists of authenticating and authorizing a person and system per session. Plus, our complete safety portfolio additionally evaluates endpoint well being, facilitates remediation, and attributes all knowledge accessed and exchanged all through the session with the originating entity.
Comply to Join and Cisco ISE
For many authorities organizations, complexity usually surfaces from deploying a big patchwork of instruments to mitigate varied threats. The result’s a safety surroundings with too many instruments and never sufficient specialists on workers. This implies your missions and applications face an uphill battle to successfully fight threats from quite a few assault vectors concurrently.
That’s the place Cisco Id Companies Engine (ISE) can add great worth for presidency networks. Cisco ISE is our Zero Belief coverage engine and coverage determination level (PDP). It’s a foundational part of Zero Belief and an exceptionally versatile part of a complete technique when paired with different instruments, making contextual entry selections and implementing coverage repeatedly all through every session.
Cisco ISE integrates with main third-party id platforms, endpoint options, and different varied knowledge sources to supply contextual and risk-based entry to operational environments for each customers and gadgets. It might probably additionally make selections whether or not the session originates over conventional wired and wi-fi networks, P5G, VPN, or ZTNA use circumstances.
In a world the place most organizations are understaffed, it’s vital that applications simplify their toolset to create most effectiveness. Automation and orchestration also can create their very own operational challenges if there are too many transferring components amongst distributors. That’s why we’ve additionally geared up Cisco ISE is with wealthy APIs to assist automate dynamic coverage and facilitate simplified coverage enforcement throughout safety options and community environments.
An built-in toolset for Comply to Join
When not utilizing phishing mechanisms, in the present day’s attackers depend on misconfigurations and person error for entry factors. To attain the specified outcomes and the guarantees of Zero Belief ideas, the federal government should work to streamline their toolsets to ones that combine successfully. This may assist them obtain visibility and enforcement persistently end-to-end. Safety architectures should additionally be capable to assert each least-privilege entry on the onset of the connection and risk-based updates to the session within the occasion of irregular exercise.
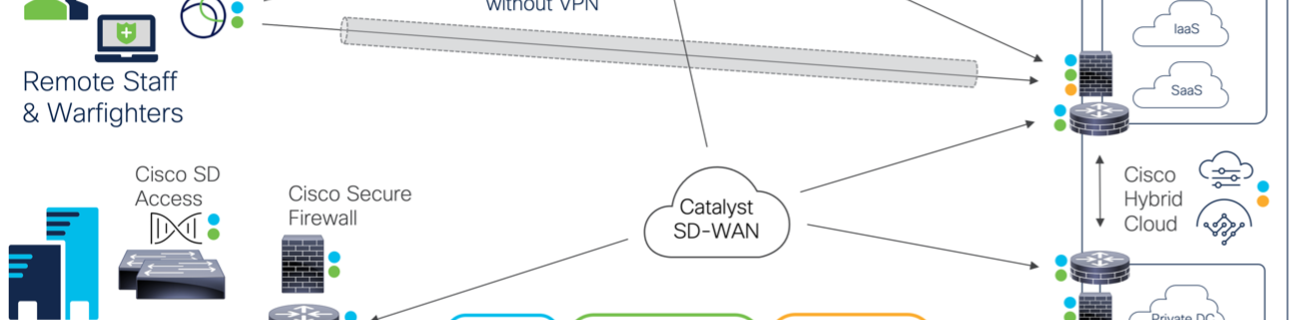
That’s the beauty of the Cisco Safety portfolio. As a vital a part of an built-in toolset, it creates a system to establish customers and property earlier than it authorizes them for entry into your community surroundings. The identical capabilities also can monitor person and system habits for abnormalities as they entry knowledge (at the side of different instruments), throughout any connection medium, and finally replace controls if risk-based updates should be utilized to the session (Determine 2). This consists of:
- Cisco Id Companies Engine (ISE), Safe Firewall, Safe Community Analytics, and Safe Consumer combining to supply visibility and enforcement for any connection try. This creates a unified and safe platform, particularly when paired with Cisco’s industry-leading community and risk intelligence capabilities.
- Cisco ISE performing as a Zero Belief coverage determination level (PDP) and integration level by way of APIs, to include third-party capabilities in a multi-vendor Zero Belief ecosystem.
- Cisco Safe Entry integrating with our Safe Consumer to supply end-to-end encryption or defend endpoints from the cloud when they don’t seem to be related to the enterprise.
Getting the appropriate instruments for C2C
As at all times, it’s vital to pick the appropriate device for the job. That is very true in terms of cybersecurity. Deploying the correct mission-aligned instruments helps your group obtain the specified return on funding (ROI) whereas growing your safety operation heart (SOC) effectivity. This can be a nice advantage of adopting Zero Belief ideas.
The capabilities of Cisco’s safety portfolio (by way of our technical alliance companions) additionally combine with a number of main {industry} distributors who present deep endpoint inspection, id lifecycle, hybrid workload and container environments, occasion correlation, and extra. This supplies your company with most effectiveness.
Bear in mind, in terms of Zero Belief it’s vital to take a look at the place to start every group’s journey to maturity. For the DoD, constructing on a long-standing historical past of RMF, Protection in depth, and NIST 800-53, Zero Belief maturity may also help facilitate collaboration between siloed organizations. The excellent news is that the Comply to Join program can be utilized as a beginning catalyst, with the fundamentals of stock and endpoint well being creating a chance to implement coverage and attribute habits to customers and gadgets persistently.
Transferring ahead, utilizing instruments that successfully carry out these features for the scope of Comply to Join, and inform different applications, is essential to turning the tide in opposition to the rising pressures of defensive cyber operations (DCO). Cisco’s Safety portfolio, at the side of a consolidated set of distributors, may also help the federal government achieve this and streamline your efforts towards a safer operational surroundings.
Extra assets
Share:

